Defense4All (previously known as OpenDefenseFlow)
defense4all
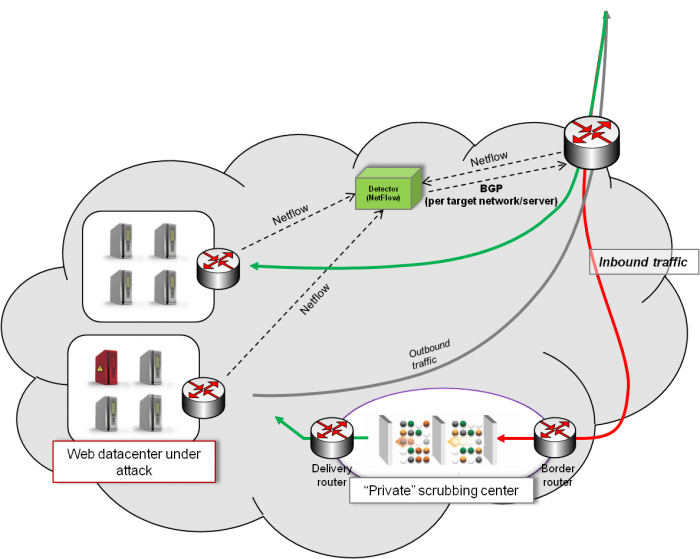
In recent years we have seen a dramatic increase in cyber-attacks, in particular Distributed Denial of Service attacks (DDoS) which attempt to bring down the targeted services by exhausting the service compute and/or network capacity. These attacks can impose a real threat to the economy; market studies show that, financial organizations lose an average of 0.5% to 2.5% of annual revenue due to security-related downtime. Hence, there is a growing need for efficient mechanisms to detect and mitigate the effects of those attacks. Protection against DDoS attacks in Out-Off-Path (OOP) systems consists of three steps: 1) collection of traffic statistics and behavior, 2) detection of anomalies (suspicions of attacks), and 3) mitigation (traffic cleansing, selective source blockage, etc.). Traditionally, OOP DDoS attack protection solutions use Netflow for statistics collection and BGP to divert the infected traffic to a “scrubbing center” where the mitigation equipment cleans it up and then returns the valid traffic to the target servers, as shown in the following figure, where red lines represented infested traffic, while green lines represent clean valid traffic:
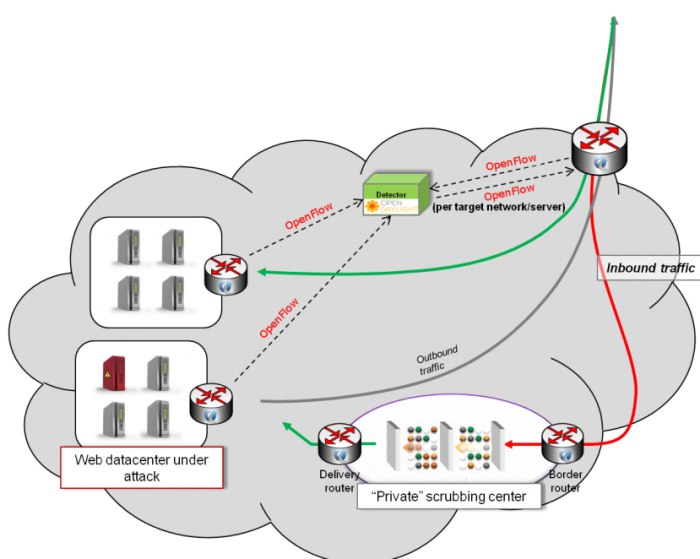
There are several limitations to the Netflow/BGP approach to DDoS mitigation, in particular long detection times, as well as lack of granularity in selecting traffic to divert (BGP diversion is limited to L3 addresses only). Moreover, to avoid routing loops, these solutions usually require the establishment of tunnels (MPLS, GRE, etc) which impact performance and add complexity. We can overcome these limitations with SDN:
The Defense4All project will provide to OpenDaylight a system for attack detection and traffic diversion (steps 1 & 2) above, based purely on monitoring and control capabilites exposed by OpenDaylight. As an attack detection tool Defense4All will function standalone, however, for actual attack mitigation (step 3) it needs to rely on specialized devices in a scrubbing center. While these devices are, at least for the time being, outside the scope of the OpenDaylight project, to provide a fully functional solution (detection and mitigation), Defense4All will include vendor-independent hooks to configure and control those devices. The entire system is shown in the following figure:
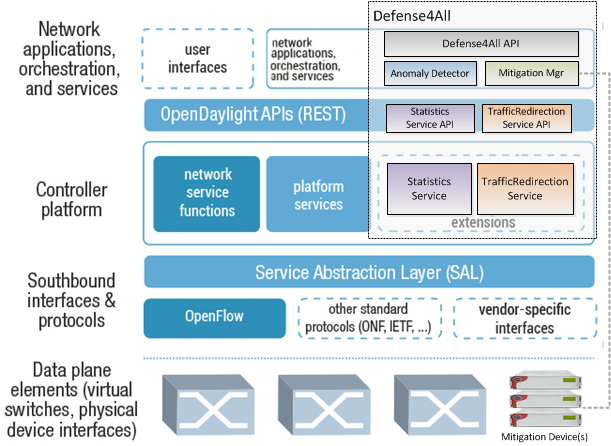
The Defense4All Anti-DoS system is composed of four major functional subsystems:
The statistics collection and traffic redirection subsystems interact with the controlled network directly, hence they will be developed as extensions to the controller platform, including extensions to the ODP NB API. The anomaly detector and mitigation manager subsystems are independent of the controlled network topology, hence constituting a “network application” (according to the OpenDaylight definitions) and, as such it will be developed on top of the Controller’s NB API. The high level architecture of the Defense4All, as well as how the different subsystems fit in overall OpenDaylight architecture are shown in the following figure:
The Defense4All will provide the following:
Who is, or will be working on this effort?
Who would be the initial committers to the project?
Inbound Code Review has been completed with no issues found. {Phil Robb: 8/1/2013}